By Luke WilladsenBLUF: This blog series is written to provide an anecdotal history of the evolution of exploitation in cybersecurity, focused largely on network exploitations in an enterprise and couched as Luke’s perspective over his decade-long career in InfoSec. To best discuss the state of exploitations in cybersecurity in 2010-2015, let’s first take a brief walk back in time to put your mind in the right timeframe. The year was 2010, and…
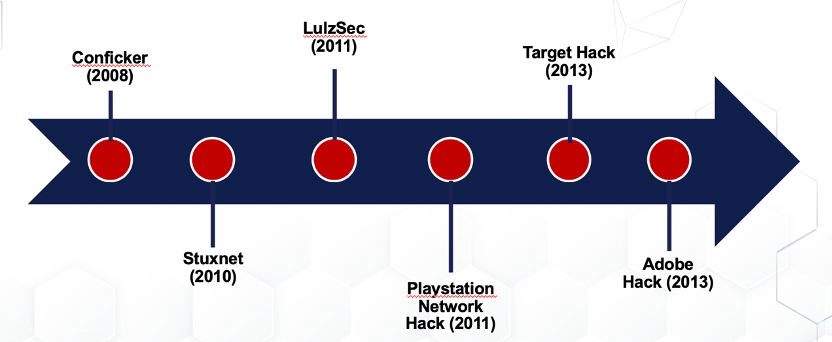
Vulnerabilities in 2010-2013 Prior to 2010, the worst thing that cyber defense teams really had to face was the Conficker worm, which spread in 2008 and leveraged the infamous MS08-067 vulnerability that took advantage of Window’s RPC service. Antivirus vendors were able to signature the worm, and Microsoft was able to patch the vulnerability. At the time, vulnerability management systems were nowhere near the capabilities we know them to have today, most organizations did not have strong patching procedures, endpoint security was strictly signature-based, operating systems gave no care as to the validity of the executables and libraries it was loading, a sizeable portion of endpoints were probably at end-of-life (ahem, Windows 2000), and by-and-large, network topology was completely flat. Simply put organizational IT security was poor, because for the most part, you could get away with it. To compound these issues, advanced techniques were being used to hack subpar networks – i.e. carving up networks with nothing but buffer overflow exploits. And then the “unthinkable” happened… The Times are a Ch-Cha-Changin’
In 2010, the Iranians discovered that something was wrong with some of their nuclear centrifuges. They investigated and found what is could be considered, a modern marvel. Stuxnet leveraged four zero-day exploits and could jump air gaps, and it scared people. StuxNet targeted a government, and showed the World just how powerful malware could be. Then the calendar flipped, and 2011 hit hard. LulzSec started smashing up anyone and everyone they could, and for the first time the private sector was targeted by large-scale cybercrime. Profits were lost and reputations were damaged. This wasn’t a particular single exploit or vulnerability, but instead the work of numerous individual actors. And while business owners may not have been losing sleep over StuxNet, they now had to recognize that extremely advanced malware could be created and disseminated in a way it had never been seen before. But the first half of the decade wouldn’t end without several more, vastly harmful breaches. Playstation Network (PSN) suffered a General Network Failure and the theft of 77 million PSN user accounts and associated financial info, and the high-profile attacks on Target and Adobe launched the cybersecurity community into a full-on panic. Where Do we Go from Here? The exploitation chain in a standard hack or penetration test is normally as follows: gain access to a system > elevate access to SYSTEM/ admin/ root > pilfer > move on to next system. At the time, this could often be conducted via a simple buffer overflow and without looking for non-admin credentials. But rather than throw our collective computers away because they were too insecure, instead the cybersecurity community was treated to something rather special. Many organizations started taking their cybersecurity posture and practices much more seriously. Security product vendors stepped up their game as well. Endpoint security became more than signature matching, monitored the network stack, and could detect incoming buffer overflows. High-quality heuristics that could monitor changes in the operating system were introduced. Cybersecurity professionals looked into how Windows actually works and took note of what executables, libraries, and services needed to be protected. Microsoft delivered improvements to Windows Defender, turning it into a force to be reckoned with. Firewalls got better. IDS/IPSs were installed and properly configured. Organizations took to monitoring and understanding the complex logs that their systems generate and began using analytics to scour these logs for indications of intrusion though tools like SIEMs. Developers got better, too, as more of them started using secure coding practices and testing their code/ products for security before release. Things were looking up for the defenders, and so naturally, hackers had to adapt. It was now harder to remain undetected when attempting to breach systems. You may not believe this, but the hacker community responded the opposite way than you’d think. With security products now catching non-zero-day buffer overflow attempts and complex persistence mechanisms, hackers actually reduced the complexity of their attacks. Seeing no reason to spend their time and effort designing more advanced and elaborate techniques that kept getting caught and signatured through heuristics, hackers started simplifying attacks and relying on human error and the burden of managing massive information systems. In part 3, Luke tackles the rest of the 2010’s and discusses into the future of exploitation. About the Author: Luke Willadsen, Technical Services Lead, EmberSec, is an InfoSec professional and white hat hacker. After getting his start with the Dept. of Defense in 2010, Luke leveraged his specialization in offensive security and eventually turned to private and public sector consulting. Mr. Willadsen has a bachelor’s degree in cybersecurity, a master’s degree in technology studies, an OSCP certification, and a CISSP certification. Outside of his professional life, Luke is a husband, an animal lover, a fitness enthusiast and a passable guitar player, plays a bard in Dungeons and Dragons, and enjoys playing a few rounds of Battlefield on my PS4 a night or two a week. About EmberSec: EmberSec, a Division of By Light, serves as a provider of advanced, technical cybersecurity services and solutions. Whether that's testing the maturity and efficiency of your security program through technical assessments, integrating highly customized Managed Detection & Response capabilities, or aligning your infrastructure and security practices around industry frameworks, EmberSec understands the complexities involved in establishing a truly secure enterprise. The EmberSec team is comprised of senior security researchers, operators, and intelligence professionals, and specializes in the following domains: Comments are closed.
|
|
© 2020 By Light Professional IT Services LLC. All Rights Reserved.
|

 RSS Feed
RSS Feed
